Rulemaking Timeline for CMMC DFARS Rule
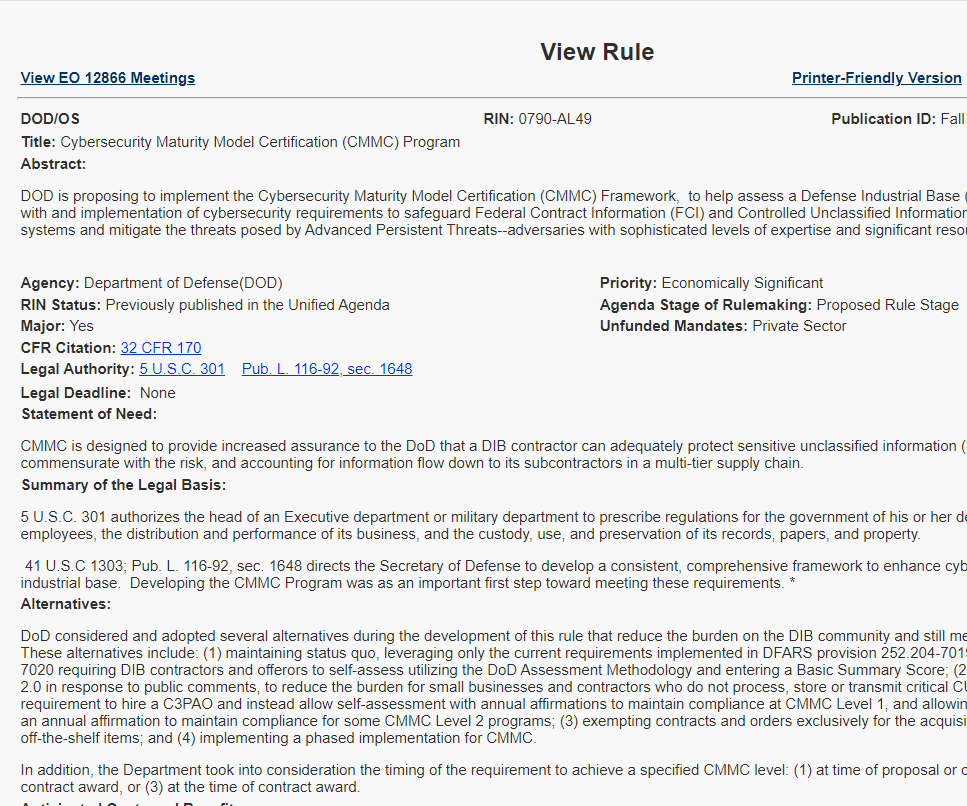
The proposed CMMC Rule has been submitted to the Office of Information and Regulatory Affairs. Several groups (mostly cybersecurity professionals) have met with DoD CIO and OIRA to give recommendations for the rule. Most of them submitted documents with their feedback which can be downloaded from the EO 12866 page here.
Disclaimer: This article is primarily speculation and opinion about current CMMC news and the upcoming DFARS rule for CMMC. Official guidance on CMMC is provided by the Department of Defense.
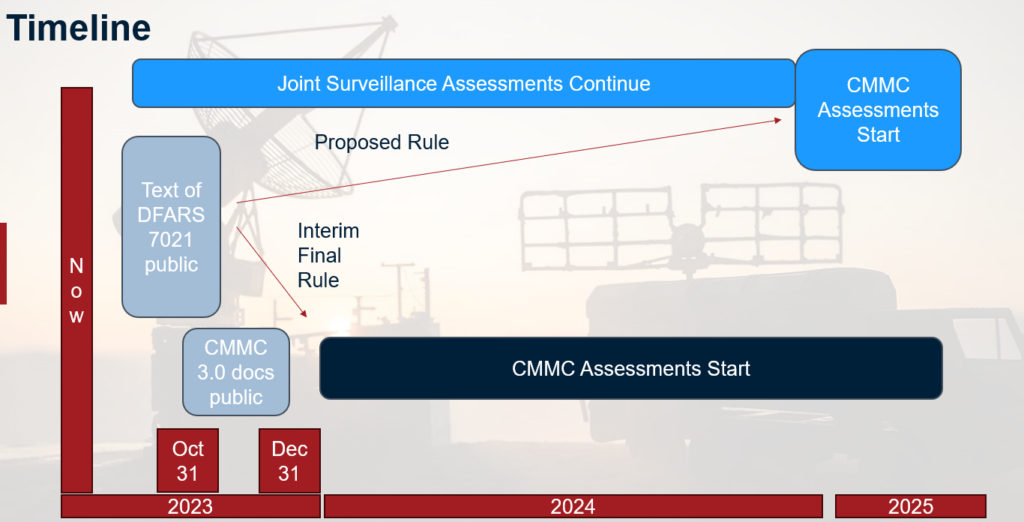
Almost everyone thinks that the rule will come out as a “proposed rule”, which means that the rule will be made visible for review, but cannot be applied to new or renewing contracts for another year or so. Comments can be submitted once the rule is visible, but historically it is very unlikely that substantial changes would be made.
The other option is an “interim final rule”, which means that the rule will be made visible for review on the same timeline, but it can be applied to new and renewing contracts 60 days later. Comments can be submitted once the rule is visible, but there won’t be time for any changes to be made before the rule goes live. The rule can be altered in response to comments later, but historically it is very unlikely that substantial changes would be made.
On average, DFARS rules like this are made visible for review a few months after they are submitted to OIRA. We are starting the 4-week window when the rule is most likely to be published (made visible).
Outstanding Concerns / Predictions for CMMC
Based on DoD comments prior to starting the rulemaking process, and based upon the accidentally-published CMMC documents from August 2023, we are expecting to see the following when the rule is published.
Assessment scope expands
“Security Protection Data” will be added as a type of data that needs full 800-171 level security for the information system where it is stored. Examples of Security Protection Data are “log data, configuration data”. If things like System Security Plans or network diagrams are considered Security Protection Data, then organizations like Registered Provider Organizations will need their own CMMC Level 2 certifications, just like C3PAOs already do.
Cloud Services External Service Providers that store CUI or Security Protection Data will need FedRAMP.
Non-Cloud Services External Service Providers that perform any security function will need CMMC Level 2.
Security Protection Assets such as log servers, antivirus servers, firewalls, multi-factor authentication, configuration management databases, directory services will be assessed against all 800-171 requirements.
Still no fix for the “SPA infinite chaining” issue which has been conveniently ignored by Joint Surveillance assessments so far.
Contractor Risk Managed Assets may be assessed against CMMC security requirements if not sufficiently documented.
CMMC Level 2 assessments include verification of DFARS 252.204-7012
Over the last years, it has been a struggle to determine whether private sector assessors are allowed to inspect DFARS 252.204-7012 compliance (which requires things like FedRAMP clouds, incident reporting to DIBNET, and flow-down). In general, private sector assessors don’t feel that they can assess those topics. The upcoming rule should clarify what private sector assessors are allowed to do.
CMMC Level 3 will be formalized
This is an enhanced level of security requirements for defense contractors handling highly sensitive information, such as designs for new weapons systems.
eMASS for defense contractors
The DoD has been working on a database to track assessment results (good or bad) and CMMC certifications for defense contractors. It looks like the database is almost ready for prime time.
CMMC Level 1 and yearly attestations of compliance
We expect the rule to include a method for defense contractors to attest to their compliance with CMMC Level 1, Level 2, and Level 2 on a yearly basis. The rule will probably require an executive of the company to sign that the attestation is accurate.
Exact rules for flow-down and prime responsibilities will be published
Prime contractors are expected to be responsible for the cybersecurity of their supply chain. The rule may allow primes to pick-and-choose which subcontractors need CMMC. The rule may encourage primes to push all of their subcontractors to have CMMC certificates. It is also possible that primes will be allowed to accept third party assessment reports for their subcontractors in lieu of CMMC certificates.
Criteria for pass/fail
We expect the rule to include specific language about how many, or which, requirements can fail and still result in a CMMC certificate. We are expecting the criteria to be very strict, especially in comparison to the government’s own cybersecurity programs, which allow long-term POA&Ms.
Pick-and-choose contracts
We still expect the rule to only apply to a small fraction of contracts in the first years. It is likely that the DFARS clause will be applied to all contracts by default after a certain amount of time (3 years?).
Waivers
We expect the DoD to include a waiver process for situations where no supplier has a CMMC certificate. What is unsure is whether the DoD will allow waivers in order to choose the cheapest supplier when a certified (but more expensive) supplier exists.
C3PAOs
All the talk so far has been about building a private-sector assessment ecosystem of C3PAOs accredited by the Cyber-AB using ISO 17011 / 17020 as a model. But the Cyber-AB has struggled with their role as an ISO accreditation body. Will the rule change this model?
800-171 Revision 3
The rule will hopefully address what set of requirements are used during a certification assessment. We are worried that it will leave this topic blank, which will mean that as NIST SP 800-171 increments to new versions, it automatically is applied to new and renewing contracts with no time to transition.
Should I make big changes now?
We are so close to seeing the text of the rule. All indications are that assessment scope will increase and industry leaders will want to position themselves as safely as possible (migrating away from external providers that will cause assessment failure, for example). However, it makes sense to wait a few weeks and see for sure before committing major funds or impacting your organization.
Will the rule just change again in the future?
I asked Jacob Horne, the industry’ subject matter expert for the CMMC DFARS rule.
Q: “It is two weeks from now, the CMMC rule is published, and we don’t like what it says. Should we keep waiting for another update?“
A: “Substantial changes to a rule would require the rulemaking process to start over from the beginning. The rulemaking process involves numerous reviews, analyses, and substantial inter/intra-agency coordination prior to regulatory review by OIRA. All of this is prior to publication for public comment. If the substance of a rule changes, then those processes need to be re-done. This means that published rules are extremely unlikely to change and any changes that do occur are usually superficial. The great irony about the rulemaking process is that the whole thing takes so long because of all the checking and reviewing that goes on to ensure that the public can comment on exactly what the government plans to do. However, by the time a rule is published it is so locked-in that public comments have little leverage over changing it.“
What is your projection? Did this article leave out a big change or expectation? Do you intend to take the published rule at face value, or plan to wait to see how it changes?
Kieri Solutions is the sponsor for CMMCAudit.org. They are an Authorized C3PAO, passed their own CMMC Level 2 assessment by the DoD in early 2022, and are actively performing Joint Surveillance Voluntary Assessments of 800-171 compliance. Kieri Solutions offers expert assessment, preparation, and compliance documentation services. We recommend reaching out to them if you are struggling with your documentation or want to get in the queue for a CMMC Level 2 assessment.
In order to participate the contract which will issue in 2025, We have to be assessed through CMMC at least in 2024. then we have to request the assessment to the CyberAB and make a contract with one C3PAO in this year or next year early. But The law or regulaton is not publicly implemented. Is it possible to be assessed at level 2 unger this environment even if our company is ready to be assessed in managerially and terchnically?
As you said, it isn’t possible to be formally assessed against CMMC Level 2 right now, because the regulation isn’t effective. The Joint Surveillance Voluntary Assessment program is a method to get assessed now, which should qualify you for CMMC Level 2 certification as soon as it is available. Check our C3PAO sponsor: Kieri Solutions, if you’re curious about Joint Surveillance.
The CMMC Process involves a lot of policies, procedures, appointment letters. Will these templates be made available to the public sector in accordance with eMASS Formatting, or other Government (DOD) Formatted documentation?
The DoD has been cautious about telling companies exactly how to implement the requirements because that could cause market upheaval. So for policies and procedures, very unlikely. Regulations and official requirement documents have been provided in forms that people can copy-paste from, or input via text interpreter. I recommend asking them for specific formats as part of public comments, they’ve been accommodating when they realize we need it.