In today’s rapidly evolving cybersecurity threats, the United States Department of Defense (DoD) has taken a definitive step to bolster the security of its information networks, especially those handled by contractors. This initiative, known as the Cybersecurity Maturity Model Certification (CMMC), marks a significant shift in the DoD’s approach to ensuring the digital security of Controlled Unclassified Information (CUI).

Why CMMC is Important for Cybersecurity
The Cybersecurity Maturity Model Certification (CMMC) has become a critical framework for strengthening the cybersecurity of organizations handling sensitive information for the Department of Defense (DoD). Previously, contractors working with Controlled Unclassified Information (CUI) only needed to self-certify compliance with NIST SP 800-171. However, this approach left networks vulnerable, resulting in data breaches and cyberattacks.
By introducing CMMC assessments and audits by third-party assessors (C3PAO), the DoD ensures that contractors meet rigorous cybersecurity standards, improving the defense supply chain’s overall security.
Why CMMC is crucial for cybersecurity:
- Protects sensitive DoD information
- Prevents cyberattacks on contractor networks
- Increases accountability through CMMC audits
- Ensures compliance with evolving DoD CMMC requirements
- Strengthens the defense industrial base against emerging threats
Implementing CMMC consulting services or working with a CMMC assessor helps contractors close gaps in their cybersecurity practices, ultimately reducing the risk of successful attacks. The shift to third-party audits under the CMMC framework emphasizes the importance of robust, verified security controls to protect critical information.
This new certification model enhances trust, collaboration, and the security posture of organizations involved in national defense operations. By requiring all DoD contractors to adhere to higher CMMC cybersecurity standards, the certification plays a key role in safeguarding both government and contractor data.
Who is Subject to a CMMC Assessment?
The Cybersecurity Maturity Model Certification (CMMC) assessments are primarily targeted at companies and organizations that are contractors or subcontractors for the United States Department of Defense (DoD). This includes a wide range of businesses that work directly with the DoD or are part of the defense supply chain at various levels. Essentially, any entity that handles or processes Controlled Unclassified Information (CUI) is subject to a CMMC assessment. CUI encompasses a broad category of information that, while not classified, is sensitive and requires protection under federal laws and regulations. CUI data will be released to those with a level 2 certification. Support organizations that store, process or transmit CUI or provide security protections to the contractors CUI environment will be in scope. For instance, a managed service provider or security consulting firm.
It’s important to note that the requirement for CMMC assessment extends beyond primary defense contractors to include smaller subcontractors as well. This means that even smaller businesses, which might be several tiers removed from direct DoD contracts but still contribute to support of the defense supply chain, need to be CMMC certified. The final rule is expected to be out in late 2024 and assessments required in contracts in 2025. The level of CMMC certification required (ranging from Level 1 to Level 3) varies based on the type and sensitivity of the information handled by the contractor.
Understanding CMMC Levels and Requirements
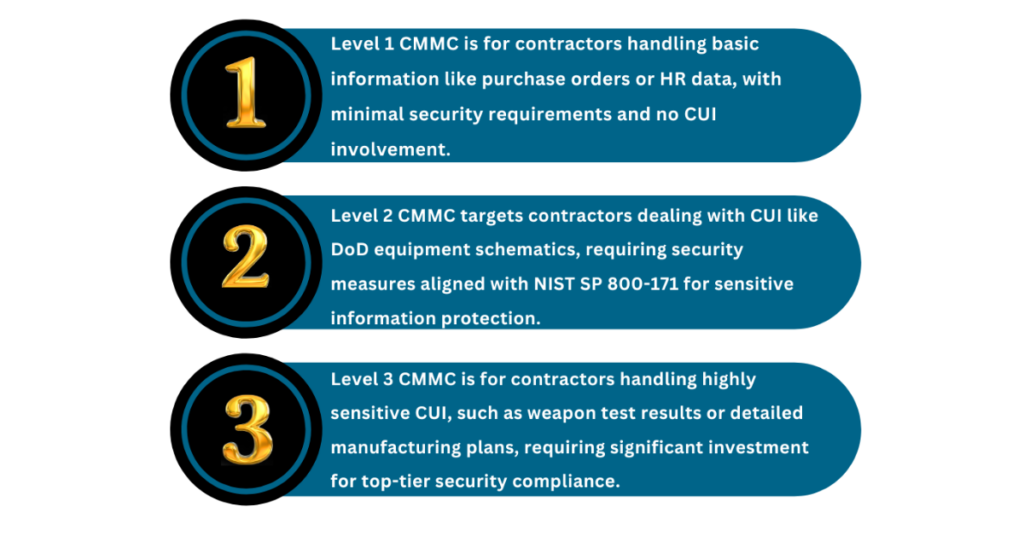
The CMMC framework is designed to ensure that contractors handling sensitive government data maintain robust cybersecurity practices, with three distinct levels that escalate in rigor based on the type of information being protected.
Level 1: Basic Cyber Hygiene
At this foundational level, contractors with minimal exposure to Controlled Unclassified Information (CUI) need to implement basic security practices. This includes measures like antivirus software, simple access control, and password protection, making it accessible to smaller businesses like resellers.
Level 2: Advanced Cybersecurity Practices
Contractors who handle CUI, such as equipment schematics or sensitive project data, need to meet 110 security controls based on NIST SP 800-171. This level requires third-party audits and focuses on protecting sensitive data through more advanced security measures like encryption, incident response, and vulnerability management.
Level 3: Expert-Level Security
This level is for contractors dealing with highly sensitive CUI, such as weapon designs or critical defense systems. Level 3 requires sophisticated, proactive cybersecurity controls, including continuous monitoring, threat detection, and mitigation strategies. Achieving this level represents the most significant investment in cybersecurity, given the high-risk nature of the data.
By structuring the certification across three levels, CMMC ensures that organizations can scale their cybersecurity efforts based on the sensitivity of the information they handle, promoting a secure environment across the defense industrial base.
CMMC and NIST SP 800-171: A Dual Focus
The evolving cybersecurity landscape for defense contractors necessitates a comprehensive understanding of the Cybersecurity Maturity Model Certification (CMMC) and the National Institute of Standards and Technology’s Special Publication 800-171 (NIST SP 800-171). While the CMMC is a relatively new regulation, it builds upon the foundational principles of NIST SP 800-171 and the Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012. NIST SP 800-171 is essential for protecting the confidentiality of Controlled Unclassified Information (CUI) in non-federal systems, and DFARS mandates defense contractors to implement these guidelines. The CMMC differs notably in its tiered certification model, demanding rigorous third-party assessments to verify compliance, a step beyond the self-attestation allowed under NIST SP 800-171. Currently CMMC proposed rule has been published for open comment. Once this comment period is over, slight edits and changes will be made and the final rule will be published. Once it is published the DoD will then decree it is adopting this rule and start injecting it into contracts.
Our website, CMMCAudit.org, offers an extensive array of resources in navigating both CMMC and NIST SP 800-171 compliance. These resources provide in-depth insights into the implementation and integration of both standards, aiming to help contractors not just achieve compliance but also enhance their overall cybersecurity infrastructure. From detailed analyses of CMMC levels to practical guides on NIST SP 800-171 implementation, our materials are tailored to demystify complex regulations and promote a proactive cybersecurity posture. This dual-focused approach not only ensures adherence to regulatory demands but also fosters a stronger, more resilient cyber defense mechanism within the defense supply chain.
What is CMMC Compliance? How Do I Become a CMMC Complaint?
CMMC compliance refers to meeting the cybersecurity standards outlined by the Cybersecurity Maturity Model Certification to protect Controlled Unclassified Information (CUI) in the defense supply chain. Achieving compliance requires contractors to align with one of the three CMMC levels, depending on the sensitivity of the data they handle. The certification process aims to ensure that contractors handling DoD information meet appropriate cybersecurity standards, thus reducing vulnerabilities in national security data.
To become CMMC compliant, contractors must first identify the level of certification required for their operations, ranging from basic to advanced. The process includes conducting an internal assessment to map out cybersecurity gaps, implementing necessary controls based on NIST SP 800-171, and preparing for a third-party audit by a Certified Third-Party Assessment Organization (C3PAO). Contractors must continually monitor and update their cybersecurity practices to maintain compliance, ensuring they are prepared for future audits and assessments. Partnering with a CMMC consultant can provide expert guidance through this complex process.
Who Needs to Become CMMC Compliant?
Contractors and subcontractors within the Department of Defense (DoD) supply chain are required to become CMMC compliant if they handle Controlled Unclassified Information (CUI) or Federal Contract Information (FCI). This includes companies of all sizes, from large defense contractors to smaller subcontractors and managed service providers that support DoD projects. The level of CMMC certification required depends on the type of information handled, with more sensitive data necessitating higher levels of certification.
Organizations needing CMMC compliance include:
- Primary DoD contractors
- Subcontractors providing services to DoD contractors
- Managed service providers (MSPs)
- Security consulting firms handling DoD information
- Companies dealing with CUI and FCI
Even smaller organizations, several tiers removed from direct DoD contracts, must achieve CMMC compliance if they contribute to the defense supply chain. Preparing for CMMC compliance involves understanding the level of certification needed, conducting internal audits, and implementing the necessary cybersecurity controls. By ensuring compliance, these organizations protect sensitive government data and maintain their eligibility for lucrative DoD contracts.

Tips to Prepare for CMMC
Preparing for the Cybersecurity Maturity Model Certification (CMMC) can be daunting, especially for contractors new to the process or those transitioning from the self-certification model. The first and most crucial step is to gain a thorough understanding of what data you possess, where it rests and flows. Creating a Data Flow Map is a crucial step in define the scope of your environment. Contractors should start by conducting a comprehensive assessment of their current cybersecurity practices against the CMMC standards. This involves identifying the type of Controlled Unclassified Information (CUI) they handle and determining the corresponding level of CMMC certification required. It’s also vital to develop an internal roadmap for compliance, which includes training staff, updating or implementing new cybersecurity policies, and establishing a continuous monitoring process to ensure ongoing compliance. Regular internal audits and CMMC assessments can also help identify vulnerabilities and guide necessary improvements in cybersecurity practices.
For those seeking expert guidance, Kieri Solutions emerges as a highly recommended partner that is an authorized C3PAO and has passed its own CMMC level 2 certification from DIBCAC. Kieri consists of an elite group of some of the most experienced and credentialed CCA’s in the industry. Many have been a part of the DIBCAC JSVA certification assessment process and understand what it will takes to achieve certification. This experience along with our set of custom documentation, enclave architecture, assessment services and consulting will give you the best chance for success Their do it yourself offerings in preparing for audits and certification is particularly beneficial for contractors aiming to navigate the complexities of CMMC smoothly.
What is a C3PAO? Do I need One?
A Certified Third-Party Assessment Organization (C3PAO) is an accredited entity authorized by the CMMC Accreditation Body (CMMC-AB) to conduct formal CMMC assessments for organizations seeking certification. C3PAOs play a vital role in ensuring that companies meet the necessary cybersecurity standards outlined in the Cybersecurity Maturity Model Certification (CMMC) framework. These third-party organizations assess a company’s compliance with CMMC levels, ranging from basic to advanced, depending on the sensitivity of the information the organization handles, such as Controlled Unclassified Information (CUI).
If your company is part of the Department of Defense (DoD) supply chain, you will likely need to work with a C3PAO to achieve certification. A C3PAO conducts an independent, unbiased audit of your cybersecurity systems to verify that your company meets the CMMC requirements for the level of certification you are pursuing. For companies handling sensitive DoD data or involved in high-stakes contracts, a C3PAO’s assessment is mandatory for certification. Once the audit is complete, the C3PAO issues the appropriate certification, allowing the organization to maintain or gain eligibility for future DoD contracts.
Working with a C3PAO is a key step in the CMMC certification process, ensuring that your company is properly assessed and can protect sensitive government data in accordance with DoD cybersecurity requirements.
Why CMMC Security is Crucial for Your Business
In today’s digital age, safeguarding sensitive data is more critical than ever. The Cybersecurity Maturity Model Certification (CMMC) was developed to ensure that contractors working with the Department of Defense (DoD) meet stringent cybersecurity standards. CMMC security is not just about protecting your organization; it’s about securing the entire supply chain against cyber threats.
By adhering to the principles of CMMC, businesses demonstrate their commitment to protecting Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). Implementing robust CMMC security measures ensures that your organization is resilient against potential breaches, giving your clients and partners confidence in your ability to handle sensitive data securely. Moreover, achieving compliance positions your business as a trustworthy partner in the competitive defense contracting landscape.
The Importance of CMMC Training for Compliance Success
Achieving and maintaining CMMC compliance can be a complex process. That’s why investing in CMMC training is essential for your team. Proper training equips your employees with the knowledge and skills needed to meet the framework’s rigorous requirements.
CMMC training programs cover essential topics, such as identifying vulnerabilities, implementing best practices, and preparing for certification audits. Tailored training ensures your team understands the specific requirements for your organization’s level of CMMC certification. Whether you’re aiming for foundational compliance or advanced cybersecurity protocols, CMMC training empowers your team to navigate the process efficiently.
By prioritizing training, your organization not only streamlines the path to CMMC compliance but also enhances its overall security posture. This proactive approach minimizes risks and positions your business to thrive in a competitive, cyber-secure environment.
Frequently Asked Questions About CMMC
Do I need CMMC compliance if I don’t handle CUI?
If your company only handles Federal Contract Information (FCI) and not Controlled Unclassified Information (CUI), you will likely only need CMMC Level 1 certification, which focuses on basic cyber hygiene. However, if your company is involved in the defense supply chain in any capacity, compliance at Level 1 is still required to meet DoD requirements for basic security standards.
How often do I need to be re-certified for CMMC?
CMMC certification is not a one-time event. Depending on the level of certification, re-assessment may be required every three years. For Level 1, annual self-assessments may be sufficient, but for Level 2 and Level 3, third-party audits by a Certified Third-Party Assessment Organization (C3PAO) will need to be repeated at regular intervals to ensure ongoing compliance with the evolving cybersecurity landscape.
What happens during a CMMC audit?
During a CMMC audit, a C3PAO will evaluate your organization’s cybersecurity practices to ensure they meet the required level of certification. This involves reviewing security controls, policies, and procedures, as well as verifying that your systems can protect sensitive DoD information. The audit typically includes interviews with personnel, documentation review, and testing of your security infrastructure.
How can I prepare for a CMMC audit?
Preparation for a CMMC audit begins with a comprehensive internal review of your cybersecurity practices. Start by identifying all systems and processes handling CUI or FCI, mapping data flows, and ensuring you meet the appropriate level of security controls. Partnering with a CMMC consulting firm can help you assess any gaps and implement necessary measures before the formal audit. Regular internal audits and staff training are also key to being well-prepared.
What are the penalties for non-compliance with CMMC?
If your organization fails to achieve the required CMMC certification, it will be ineligible to bid on or renew DoD contracts. This can result in a significant loss of business opportunities. Additionally, failure to meet cybersecurity standards could expose your company to data breaches and legal liabilities if sensitive government information is compromised. It’s essential to achieve and maintain compliance to avoid these risks.
Can I upgrade my CMMC certification level after initial certification?
Yes, if your company’s operations change or you take on contracts that require handling more sensitive data, you can pursue a higher level of CMMC certification. This process involves implementing the necessary security controls for the new level and undergoing a re-assessment by a C3PAO. It’s advisable to work with a CMMC assessor or consultant to ensure a smooth transition to a higher level of certification.
What is the role of a CMMC consultant?
A CMMC consultant helps companies navigate the complex requirements of CMMC compliance. Consultants provide guidance on implementing the necessary cybersecurity measures, conducting internal assessments, and preparing for third-party audits. They offer expert insights to close any gaps in your security practices, ensuring you meet the required CMMC level and avoid common pitfalls that could lead to audit failure.
Can small businesses achieve CMMC certification?
Yes, small businesses are required to achieve CMMC certification if they work within the DoD supply chain. The DoD has structured the CMMC levels to be scalable, meaning even small contractors that handle basic information can achieve Level 1 certification with relatively minimal investment. However, businesses handling CUI will need to comply with higher levels of certification, which may require more robust security measures.
How is CMMC compliance related to IT security consulting?
CMMC compliance is closely tied to IT security consulting because many companies need expert guidance to meet the stringent security requirements of the framework. IT security consultants can help design and implement the cybersecurity systems required for certification, including data encryption, access control, and incident response planning. They also ensure ongoing compliance by conducting regular reviews and updates as cybersecurity threats evolve.
Will CMMC certification help with other cybersecurity standards?
Yes, achieving CMMC certification often aligns with other recognized cybersecurity standards such as NIST SP 800-171 and ISO 27001. The robust security measures implemented for CMMC compliance can improve your organization’s overall cybersecurity posture, making it easier to comply with additional regulations in both the public and private sectors. It positions your company as a trusted partner, not just for government contracts but also for private clients concerned with data security.
When will CMMC become fully enforced?
On October 11, 2024, the Department of Defense (DoD) released the Final Program Rule for its Cybersecurity Maturity Model Certification (CMMC), formalizing the assessment and compliance requirements for contractors handling Controlled Unclassified Information (CUI) and Federal Contract Information (FCI). This rule allows Certified Third-Party Assessment Organizations (C3PAOs) to begin conducting assessments. However, CMMC contract requirements will not be fully enforced until the CMMC Clause Rule is finalized, which is expected in 2025. Contractors can use this time to prepare for compliance before the rule becomes mandatory.
