Hello all, here is the news from the last few weeks. Not a whole lot going on in public or officially, but it feels like we are getting close to some major milestones.
CMMC Town Hall from February
https://cmmcab.org/videos/cmmc-town-hall-february-2021/
According to last month’s CMMC Town Hall, the DoD is actively working on defining scope.
OT out of scope?
One of the DoD engineers verbally mentioned that OT (Operational Technology, AKA factory equipment) would be out of scope for CMMC Phase 1, but that it would be in scope for CMMC Phase 2. My impression was that Phase 2 would be in several years, probably around 2025-2026, but I don’t recall if this was specifically said. Take this at your own risk until the DoD releases scope guidance in writing.
Opinion: This is great news for the manufacturers, but the R&D companies are still wondering what to do. It is almost impossible to perfectly apply CMMC level 3 protections against development labs. If anyone from the DoD is reading this, please take development labs out of scope for phase 1 too. This isn’t to say that people should run their factory or R&D equipment in the same network as their employees check email and browse Facebook. There need to be practical protections like a separate network. But 130 CMMC practices against an R&D environment is going to kill these companies.
Submitting hashed evidence to appeal assessment findings?
During the eMASS presentation in the town hall, there was mention that no copies of evidence would be captured by the assessor. Instead, the plan is to capture signatures of evidence (using hashing algorithms) then expecting the contractor to save their evidence in case of appeal.
Opinion: From the assessor point of view, I’m concerned about this idea. It is VERY easy to accidentally change a file just by viewing it (was your auto-save turned on? Your file signature just became invalid). It also adds time to every single meeting to walk the client through the process of saving evidence and running a hashing algorithm against it.
I’m concerned that this security measure is going to create a 5-10% increase in cost and cause many appeals to be rejected because the evidence appears to be tampered with. It also greatly harms the ability for C3PAO in-house quality leads to give input before a certification decision is made.
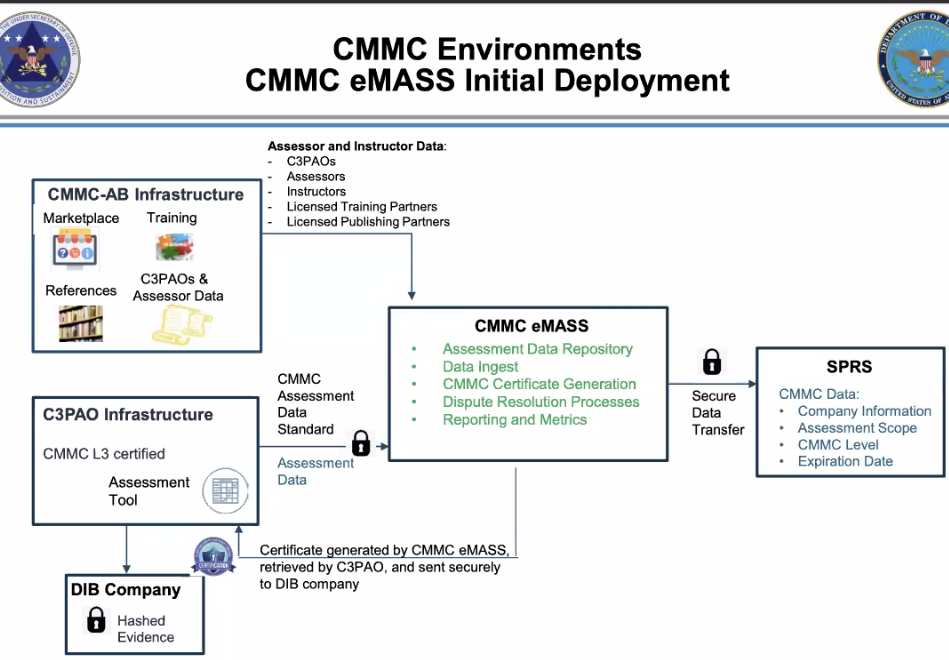
eMASS Slide from the February CMMC Town Hall
Next Town Hall – March 30th
https://zoom.us/webinar/register/WN_3M9aG3ARTa6m8OiIYXCpPQ
This is the registration link for the next CMMC-AB and DoD town hall.
A little bit of fun on the topic of CUI
Credit: Cooey Center of Excellence
CMMC Accreditation Body Update
Board changes
https://www.fedscoop.com/cmmc-accreditation-body-board-member-departures/
Ben Tchoubineh, the chair for the Training Committee, is starting the process of training his replacement and stepping down. He has been extremely active as a full time volunteer with the AB for about 15 months straight and deserves some recognition.
Nicole Dean also stepped down. She was also a founding board member, but was less visible to the public than Ben. Thank you for your efforts, Nicole!
This is old news, but in case you haven’t heard, Jeff Dalton became the Vice-Chair (#2) board member about a month or two ago. At least part of Jeff’s oversight is the governance processes and guidance for C3PAOs to ensure high quality assessments.
The CMMC-AB might be accepting self-nominations for board members. Read the bottom of this page for more info: https://cmmcab.org/board-of-directors/
Bad actors in the CMMC ecosystem
If you see a CMMC-badged professional or organization making false claims or causing harm to their clients, the CMMC-AB requests that you report them.
How do you report bad actors? Email cmmcsupport@cmmcab.org
CMMC Accreditation Body job postings
There are now job postings for VP, Training and Development , IT Manager, Program Manager, and Chief Financial Officer.
Stacy Bostjanick (DoD Acquisitions) stated on a webinar last week that the CMMC-AB’s CEO search is close to the end. The CEO open position is no longer posted on the career page either.
First DCMA / DIBCAC audits of C3PAOs starting
The DoD is starting to schedule / perform CMMC ML3 assessment of C3PAOs.
Opinion: The standard for CMMC assessments (as trained to the Provisional Assessors) is to give a 90 day remediation window to fix problems. I wouldn’t be surprised if all C3PAOs end up needing this 90 day window because CMMC level 3 is so exacting. That timeline, plus the requirement for Tier 3 background investigations of the entire assessment team, still puts us several months away from assessments.
The marketplace for C3PAOs and PAs is a bit misleading.
This is worth noting because we might have some C3PAOs authorized to work soon.
At this time, the marketplace listing shows that PAs and C3PAOs have completed the CMMC-AB processes. It does not indicate whether they’ve completed the vetting required by the DoD. Make sure that your PA has achieved their Tier 3 background investigation (a C3PAO should not offer them as part of a team until this is done). Make sure your C3PAO has gotten their ML3 certification (the C3PAO should not offer assessments for certification until this is done).
There is some talk about updating the marketplace or individual listings to show when the C3PAO or PA is fully authorized to work, but that is still in the brainstorming stage.
To my understanding, it is completely fine for C3PAOs and PAs to offer non-certification gap analysis and consulting right now. Defense contractors SHOULD take advantage of this while they are waiting to start real assessments.
CMMC acceptable solutions and architecture
Terminal Services Disagreement – is endpoint in scope?
This LinkedIn poll asks my connections (almost entirely cybersecurity professionals) whether they consider Virtual Desktop Infrastructure / Terminal Services to be a sufficient boundary to keep endpoints out of scope for CMMC Level 3. The poll makes it very clear that the solution is configured correctly to prevent copy-paste or other transfer methods, and that only video / keyboard / mouse signals are transmitted.
The amazing part of this is the level of disagreement in the community. It is almost exactly 50-50 on whether VDI is acceptable or not. We have CMMC Provisional Assessors and Registered Practitioners on both sides of the argument.
If I had just spent the last year and a million dollars building a CMMC enclave that is based on VDI / Terminal Services, I would be losing my mind at this poll. I can tell you there are many medium and large defense contractors in this exact position.
Encryption Disagreement – is FIPS validated enough to protect data in public?
https://www.linkedin.com/pulse/when-encryption-enough-vincent-scott/
This article by Vince Scott is the result of a similar poll about whether FIPS validated cryptography can be used to protect data in untrusted environments (such as non-FedRAMP clouds). Again, this resulted in wide disagreement in the community.
DFARS Cyber FAQ? This illustrates the need for guidance
These two topics illustrate a big problem in the current Provisional Assessor and C3PAO capabilities. The Provisional Assessors are expected to bring their significant years of experience to bear on technical questions like this. But 20+ years of experience doesn’t mean consistency.
Many people think the DoD’s scoping guidance will solve these questions, but I have my doubts. Existing scoping guidance in DFARS 252.204-7012 and NIST SP 800-171 is very simple and doesn’t touch on these architectural topics.
The DFARS Cyber FAQ is probably the best option for consistency about these questions right now. Both Vince and I have submitted these questions to the DoD office responsible for the DFARS Cyber FAQ. I encourage you to do the same if you see other major topics of disagreement.
Do you think Certified Professional and Certified Assessor training will cover these topics?
Thanks for the read. Please comment if you can share any news about the CMMC this month!
-Amira
Thank you for your consistent reporting and sharing information Amira. The posts are always worth reading.